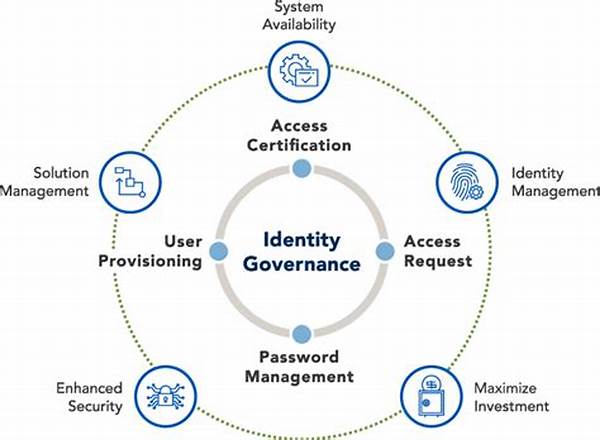
Identity governance plays an increasingly crucial role in today’s digital landscape, where the integrity and security of user identities are paramount. Secure identity governance frameworks are essential tools for organizations aiming to safeguard sensitive information effectively. These frameworks provide structured processes and technologies that help manage digital identities, ensuring that only authorized individuals have access to the appropriate resources at the right time.
Read Now : College Alumni Job Placement Programs
The Importance of Secure Identity Governance Frameworks
The deployment of secure identity governance frameworks is fundamental for organizations seeking to enhance their cybersecurity posture. These frameworks ensure robust policies are in place for managing identities and access controls, thereby minimizing both internal and external security threats. By implementing such frameworks, organizations can efficiently audit, monitor, and regulate access rights across their IT environments. Furthermore, secure identity governance frameworks help in mitigating compliance risks by aligning with regulatory standards such as GDPR, HIPAA, and SOX. Organizations are thus empowered to avoid data breaches and unauthorized access, thereby protecting sensitive corporate and customer data. Ultimately, a well-deployed secure identity governance framework not only fortifies an organization’s security but also boosts its operational efficiency by automating identity and access management processes.
Key Components of Secure Identity Governance Frameworks
1. Automated Access Management: Secure identity governance frameworks facilitate automated processes that ensure prompt user access provisioning and de-provisioning. This reduces the risk of human error in access management.
2. Compliance and Audit Trails: These frameworks enable comprehensive audit trails that assist organizations in meeting compliance mandates. Secure identity governance frameworks offer reporting features that ensure adherence to regulatory requirements.
3. Risk Assessment and Mitigation: By identifying and categorizing risks associated with identity and access, secure identity governance frameworks assist in mitigating potential threats before they materialize.
4. Role-Based Access Control (RBAC): Secure identity governance frameworks utilize RBAC to assign access privileges based on job roles, thereby enhancing security and operational efficiency within organizations.
5. Identity Lifecycle Management: From user onboarding to offboarding, secure identity governance frameworks ensure a seamless and secure identity lifecycle, addressing changes in job roles or organizational structure effectively.
Read Now : Layered Looks Leading Urban Trends
Challenges in Implementing Secure Identity Governance Frameworks
Implementing secure identity governance frameworks is not without its challenges. One of the primary barriers is the complexity of integrating these frameworks with existing IT systems. Organizations often face difficulties in aligning new governance protocols with their current technology stack, which can lead to temporary disruptions. Furthermore, the dynamic nature of user roles and access requirements poses a challenge to maintaining updated secure identity governance frameworks. Organizations must remain vigilant in adjusting and fine-tuning their governance rules to accommodate changes in the workforce and emerging security threats. Additionally, securing executive buy-in and adequate budget allocation for implementing these frameworks is essential to overcoming these challenges effectively.
Best Practices for Developing Secure Identity Governance Frameworks
Developing and implementing secure identity governance frameworks require adherence to best practices to ensure optimal effectiveness and security. Begin by conducting a thorough risk assessment to identify potential vulnerabilities and determine the specific needs of your organization. Establish clear roles and responsibilities for identity and access management to ensure accountability. Regularly review and update identity governance policies to reflect changes in the organizational structure and regulatory requirements. Employ advanced technologies such as artificial intelligence and machine learning to automate routine identity management tasks and enhance threat detection capabilities. Additionally, providing ongoing training and awareness programs for employees about the importance and execution of secure identity governance frameworks fosters a culture of security and vigilance.
The Future of Secure Identity Governance Frameworks
As technology evolves, secure identity governance frameworks must adapt to address emerging security and compliance challenges. The proliferation of remote work and digital collaboration tools necessitates more sophisticated frameworks that can accommodate decentralized access needs. Future secure identity governance frameworks are expected to leverage advanced technologies like biometrics and blockchain to enhance identity verification processes. Moreover, the integration of artificial intelligence will play a pivotal role in predicting and mitigating potential security threats. In the future, secure identity governance frameworks will continue to evolve towards more intelligent, automated, and adaptive systems, providing comprehensive security solutions that align with organizational objectives while addressing the dynamic challenges of the digital age.
Summary of Secure Identity Governance Frameworks
Secure identity governance frameworks are instrumental in safeguarding sensitive information and ensuring compliance within organizations. They provide essential tools and protocols for managing digital identities and access controls, thereby enhancing security measures. By automating identity and access management, these frameworks minimize human error and improve operational efficiency. Furthermore, with the increasing adoption of remote work and digital collaboration, the importance of secure identity governance frameworks has only intensified, necessitating their continuous evolution to address dynamic security challenges. Ultimately, secure identity governance frameworks fortify organizations against existing and emerging threats, ensuring the protection and integrity of sensitive data.